
Article 9 mins
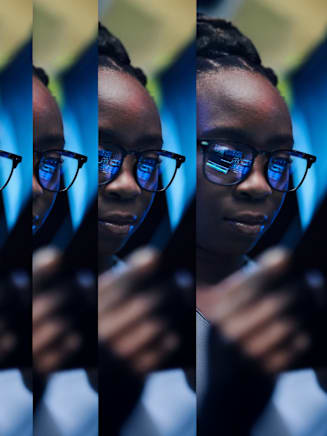
How AI and Workforce will Intersect: Navigating Risks and OpportunitiesFeatured Topics
Technology is one of four megatrends impacting global business today. Learn more below.
Report
Artificial intelligence (AI), cyber and data and analytics have helped organizations unleash operational efficiencies, connect workforces and foster growth. Yet, these advancements have also exposed companies to new and evolving risks in the race for digitalization.
Take AI, which 95 percent of global business leaders say could unleash a new wave of economic value. But the speed at which this technology is developing could also have unforeseen implications. Businesses that rapidly accelerate their operating models and embrace these new technologies will expand their digital attack surface, creating new exposures to cyber-related risks.
On the other hand, technology enables more sophisticated data management and analytics, driving better insights and informed decisions. As organizations prepare for the next technology frontier, digital tools and access to data and analytics will be critical in helping them stay ahead of the curve for both current and future risks. If harnessed and managed correctly, technology can be the catalyst that helps businesses realize their growth goals.

Cyber attacks or data breaches are the number one risk for organizations today.
Source: Aon’s 9th Global Risk Management Survey
Twenty-one percent of shareholder value can be eroded following a single cyber attack.
Source: Aon’s 2023 Cyber Resilience Report